LATEST ARTICLES
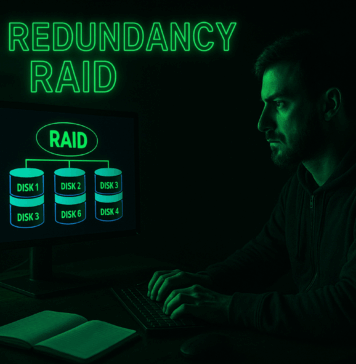
Disk Redundancy RAID
Disk redundancy through RAID (Redundant Array of Independent Disks) is a method used to protect data and improve performance by combining multiple hard drives...
TCP Flags Guide
Here’s a breakdown of each TCP flag with its purpose and for what’s used.
SYN (Synchronize) - Initiates a connection between two hosts. It’s the...
LDAP Explained
LDAP (Lightweight Directory Access Protocol) is a protocol used to access and manage directory services over a network. It is commonly used to authenticate...
Wi-Fi Standards and Protocols
802.11 Wi-Fi Standards
These refer to a set of standards for wireless local area network (WLAN) communication, developed by IEEE (Institute of Electrical and Electronics...
Web Common File Vulnerabilities
Local File Inclusion (LFI)
Local Fie Inclusion (LFI) is a vulnerability that allows an attacker to include files that are already present on the server...
Domain Controller
A Domain Controller (DC) is a critical server in a Windows-based network that manages security and permissions for all computers within the domain.
Centralized Management...
Digital Certificate Management
Certificate Authority (CA)
This is a trusted organization or entity that issues digital certificates. These certificates are used to verify the identity of websites, individuals,...
Pyramid of Pain
The Pyramid of Pain is a concept in cybersecurity that helps to visualize and understand the impact of various indicators of compromise (IOCs) on...
Cyber Kill Chain
The Cyber Kill Chain is a framework developed by Lockheed Martin to describe the stages of a cyber attack, understanding it helps organizations identify...
Access Controls
Access controls are mechanisms that manage how resources are accessed and by whom. Here are some common types of access controls:
Role-Based Access Control (RBAC)
Permissions...