What’s Log4j and Log4Shell vulnerability
Log4j is a widely-used Java-based library developed by Apache Software Foundation that’s designed to enable developers log various levels of information (trace, debug, info,...
Cyber Threat Intelligence (CTI)
This is the process of gathering, analysing, and utilizing information about potential or current threats to an organization’s digital assets focusing on understanding the...
True Positive vs False Positive vs True Negative vs False Negative
Understanding these concepts is crucial for accurate threat detection and response as it helps to evaluate and improve the accuracy of security measures, ensuring...
Detection Engineering and Its Types
This aspect of cybersecurity focuses on developing methods and strategies to detect malicious activities within an organization’s network and systems. It involves creating, deploying,...
How Tokenization Works
Tokenization is a data security technique where data is replaced by non-sensitive equivalents, called tokens. These tokens can be used in the system without...
Black Holing Made Simple
This is a network security measure used to handle unwanted or potential harmful traffic. If the traffic is unwanted or harmful, all the data...
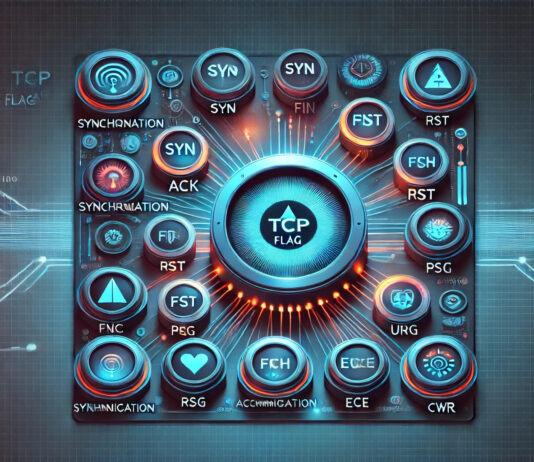
Different Types of Firewalls Explained (WAF, HBF, NBF, NGFW)
Web Application Firewall (WAF)
It’s a Firewall that operates at the Application Layer (Layer 7 OSI) that’s designed to monitor, filter and block HTTP/HTTPS traffic...